Microsoft Entra Privileged Identity Management (PIM) and FIDO2: Increasing the security of privileged roles
Privileged roles and permissions in Microsoft Entra ID allow you to manage all aspects of Microsoft Azure and Microsoft 365. To make phishing and other attacks more difficult, a secure password for privileged Microsoft Entra roles is no longer enough. Phishing-resistant multi-factor-authentication, such as FIDO2 protocol on a security key in combination with Microsoft Entra Privileged Identity Management (PIM), significantly increases security for the Microsoft Tenant and convenience for the user.
This blog post demonstrates how to configure Microsoft Entra Privileged Identity Management (PIM) using phishing-resistant FIDO2 security keys when requesting privileged roles in Microsoft Entra.
Prerequisites and Licensing
To implement phishing-resistant multi-factor-authentication when requesting privileged Microsoft Entra roles, Microsoft Entra Privileged Identity Management (PIM) and a FIDO2 security key, e.g. a YubiKey, are required. The following links shows the configuration of these prerequisites if required:
- Microsoft Entra Privileged Identity Management (PIM): Basic Configuration – cloudcoffee.ch
- Passwordless Sign In with Microsoft Entra ID (Azure AD) and YubiKey (FIDO2) – cloudcoffee.ch
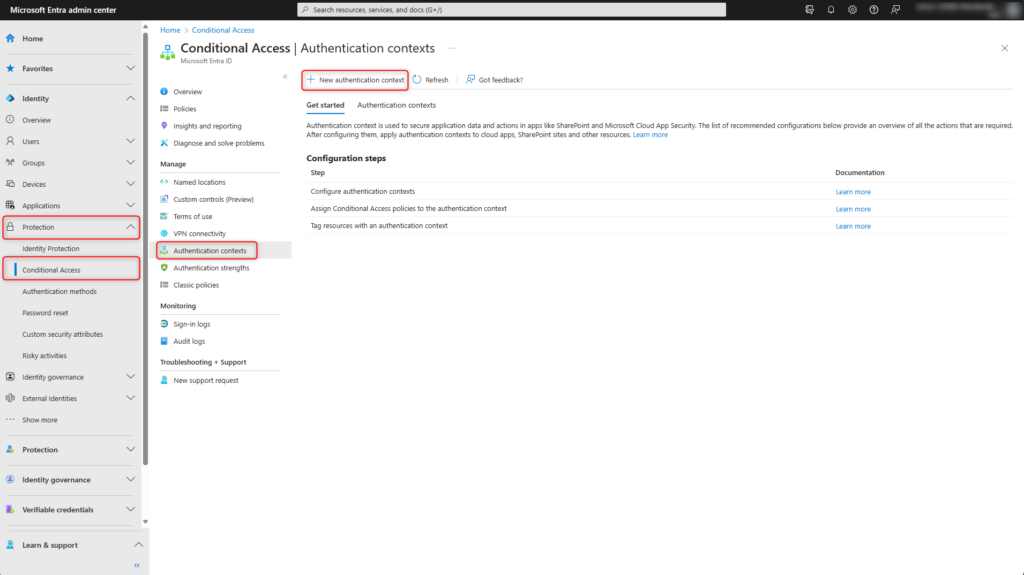
Create Authentication context
An authentication context in Microsoft Entra Conditional Access is a function for adding an additional security layer when users access sensitive data or actions. A custom authentication context is created for this purpose.
Microsoft Entra (https://entra.microsoft.com) > Protection > Conditional Access > Authentication contexts and click on New authentication context.
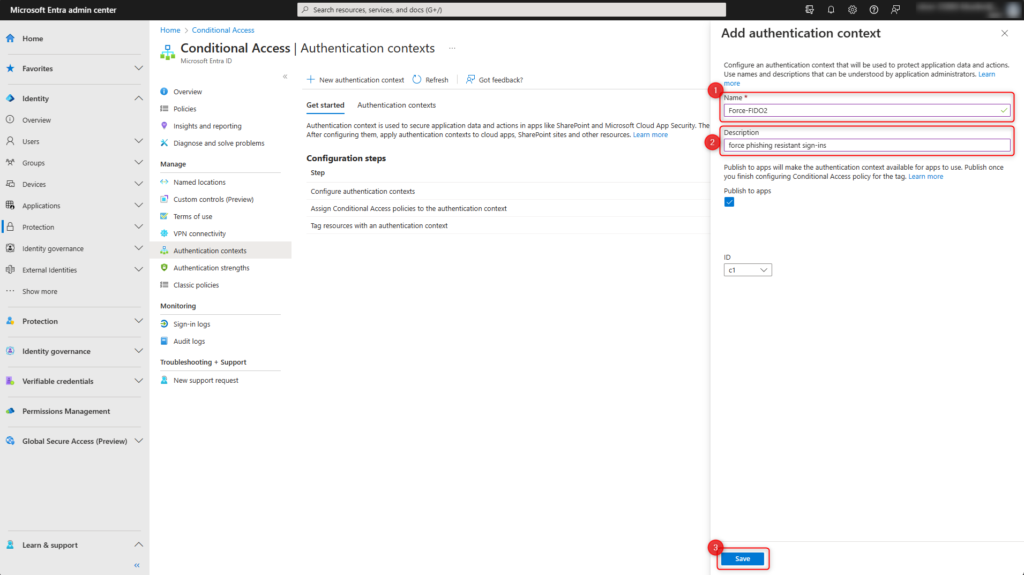
- Enter the Name for the authentication context, e.g. Force-FIDO2
- Enter detailed Description, e.g. force phishing resistant sign-ins
- Click Save
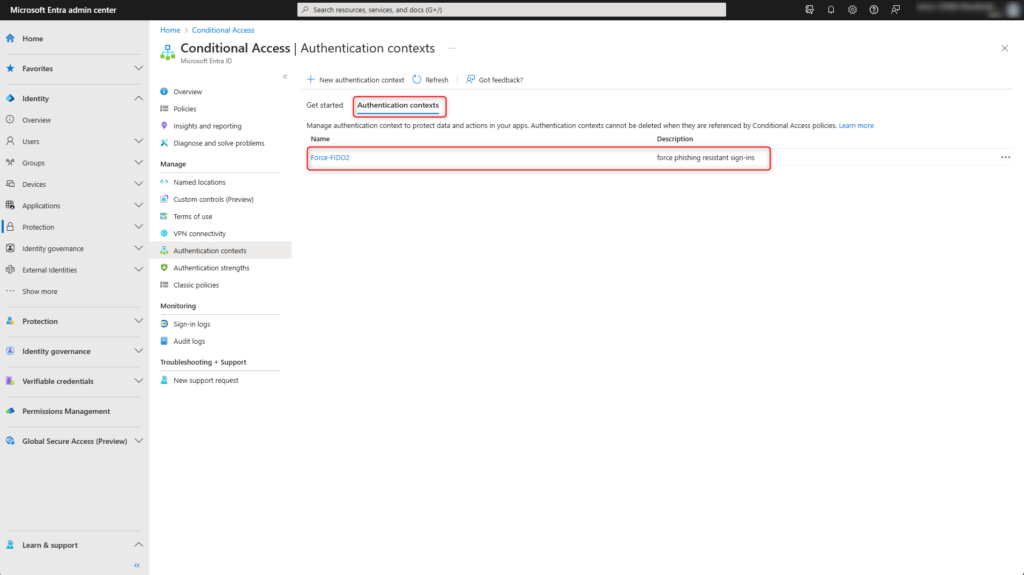
The custom authentication context is created and displayed under Authentication contexts.
Create Microsoft Entra Conditional Access policy
Microsoft Entra Conditional Access enforces phishing-resistant multi-factor-authentication when using the previously created authentication context.
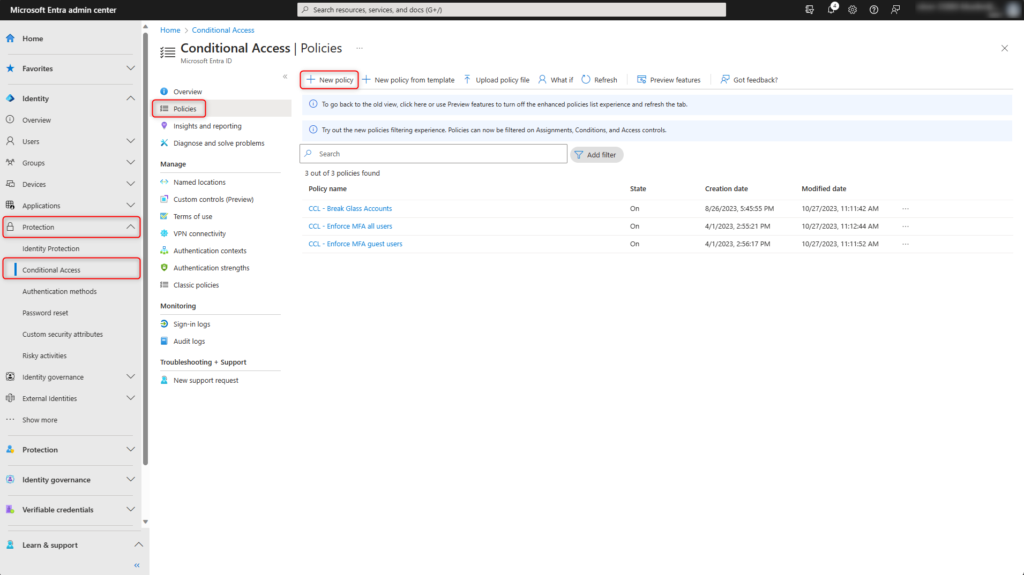
Microsoft Entra (https://entra.microsoft.com) > Protection > Conditional Access > Policies > New policy
Enter the Name for the policy, e.g. Force-FIDO2
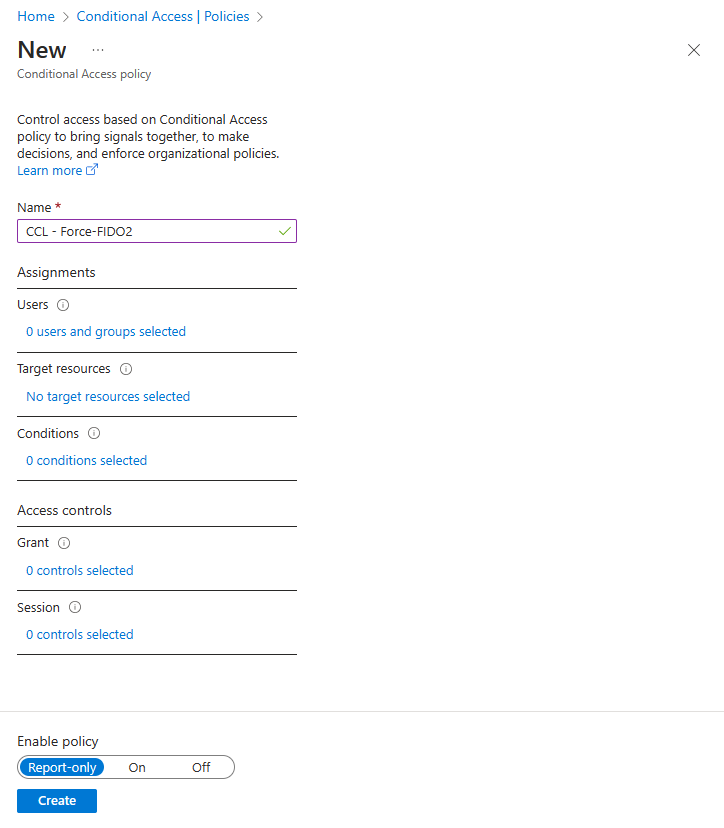
Select Users and add All users to the policy.
If necessary, exclude emergency access accounts (Break Glass Accounts).
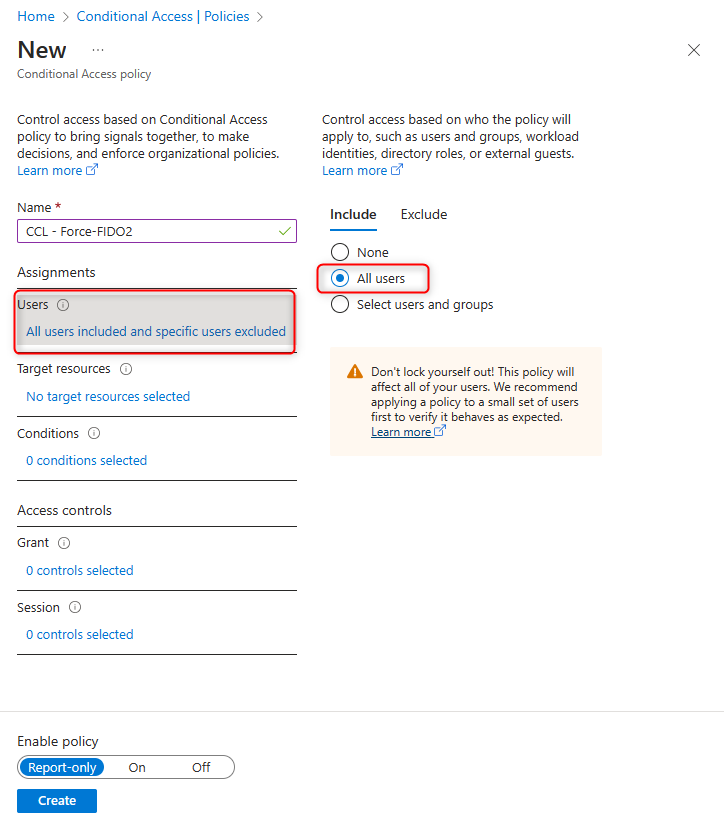
Selelct Target resources
- Select Aufthentication context
- Enable previously created authentication context
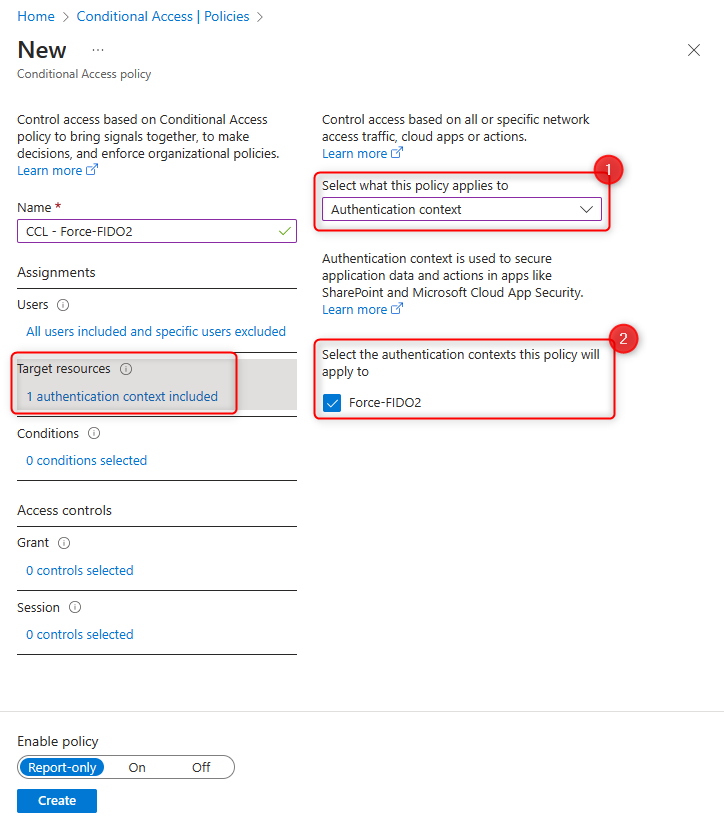
Select Grant and set Require Authentication strength to Phishing-resistant MFA.
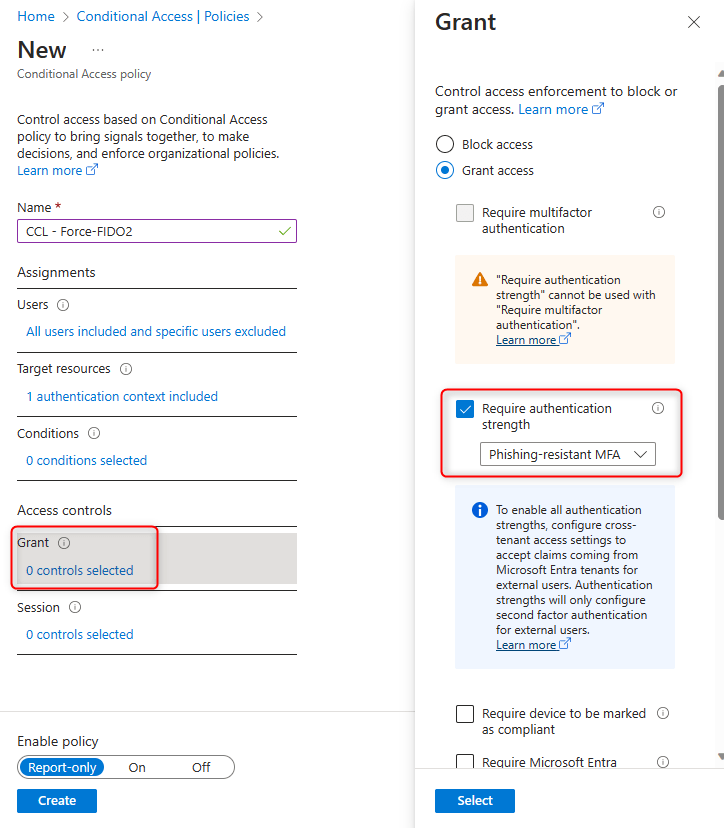
Enable the policy by setting it to On, and then click on Create.
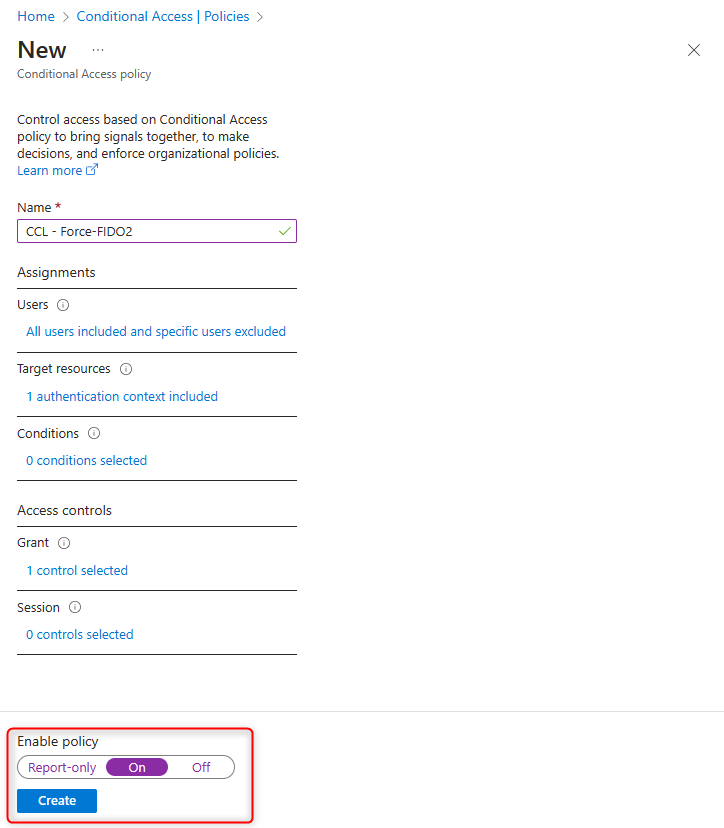
The policy for enforcing phishing-resistant multi-factor-authentication when using the authentication context has been set up.
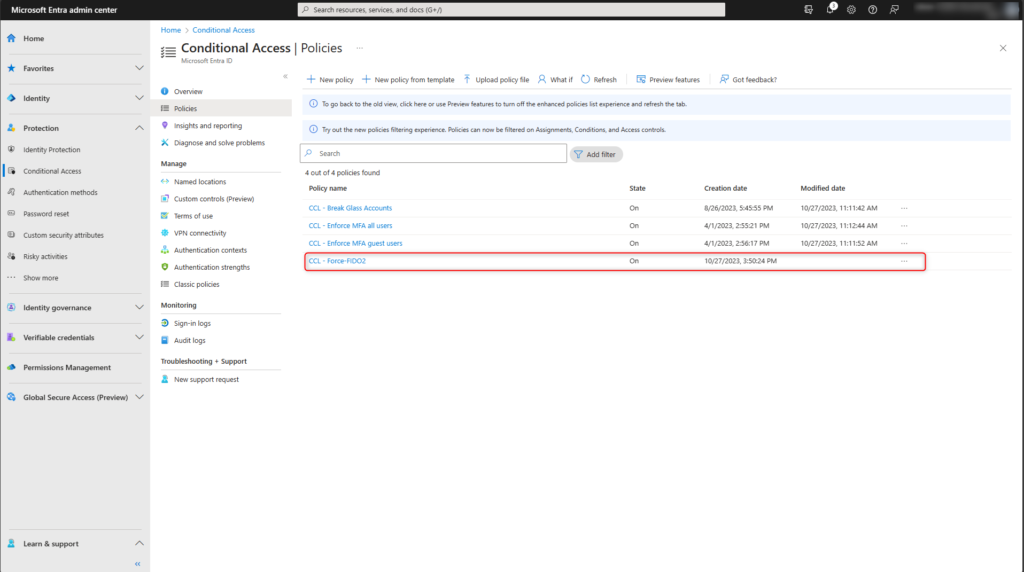
Set Up Microsoft Entra Privileged Identity Management (PIM)
The configuration adjustments for the privileged Microsoft Entra roles are now being made. These changes will result in a phishing-resistant multi-factor-authentication being required when the role is requested. In this blog post, the Global Administrator is protected with a YubiKey FIDO2 security key.
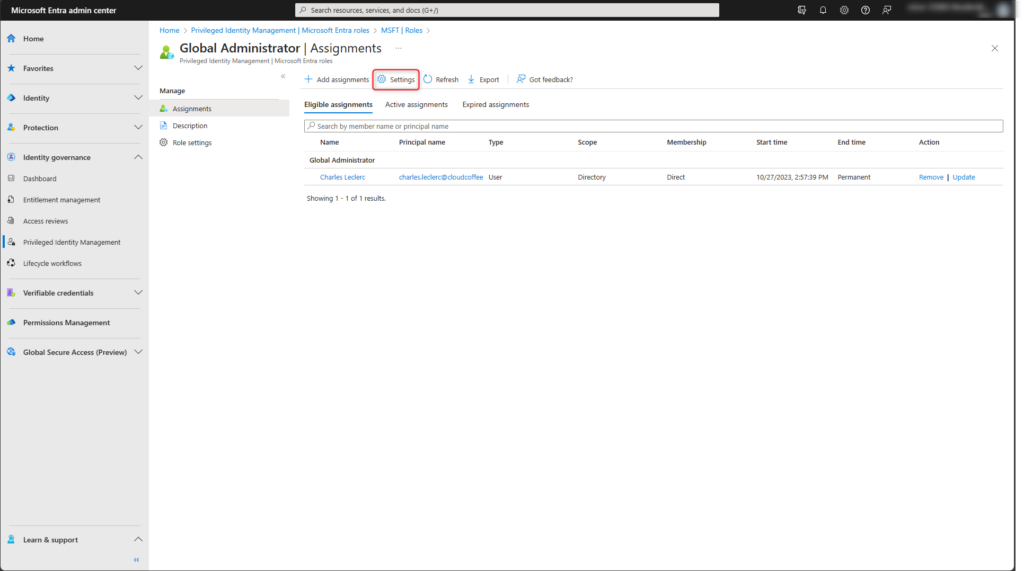
Microsoft Entra (https://entra.microsoft.com) > Identity governance > Privileged Identity Management > Microsoft Entra roles > Roles and click on Global Administrator
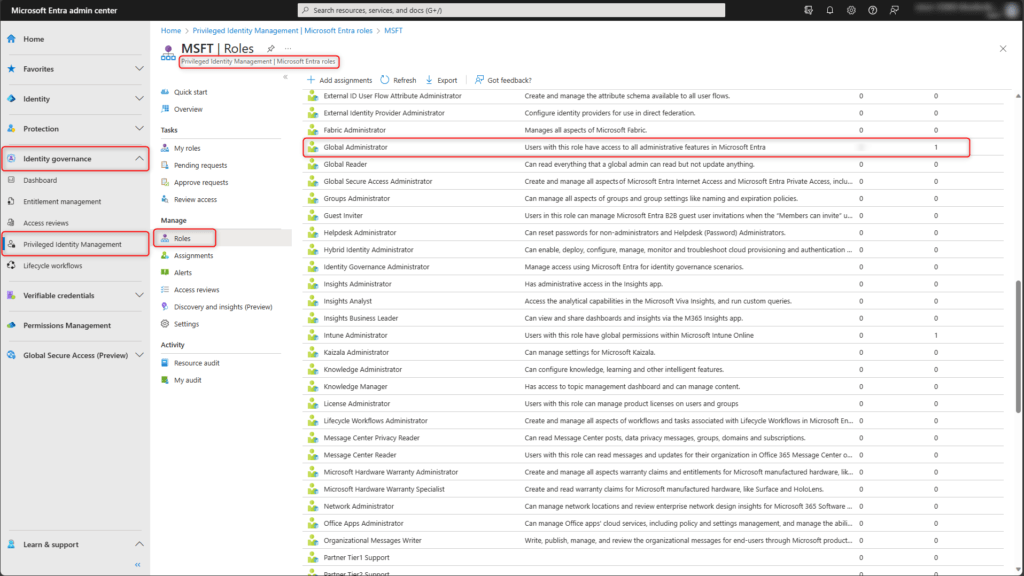
Select Settings
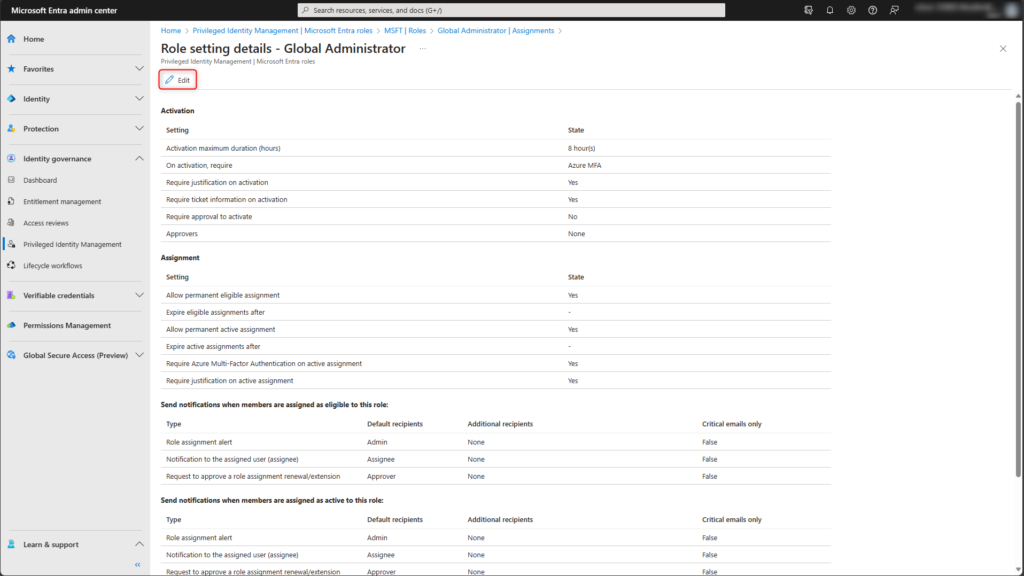
Click on Edit in the role setting details
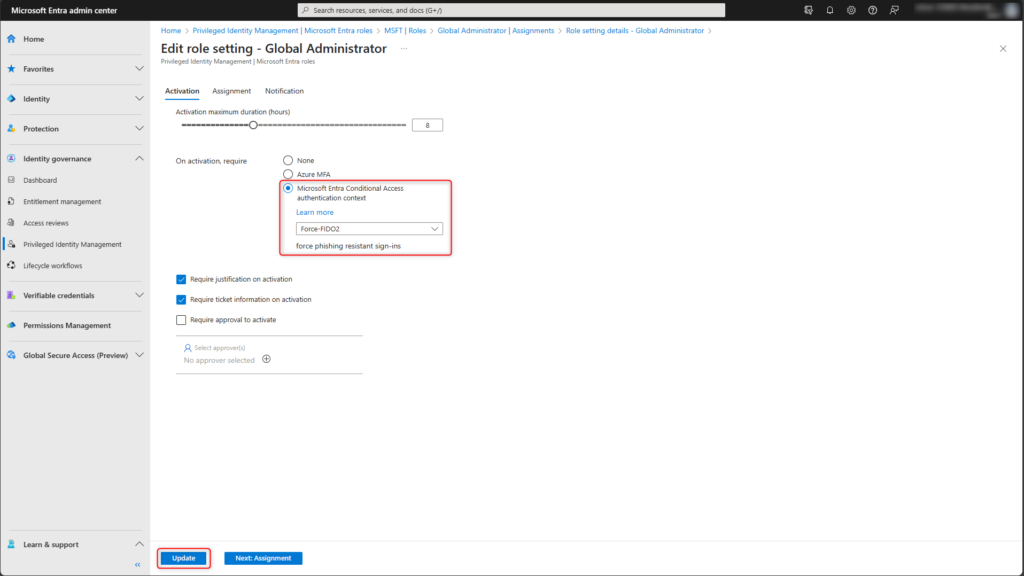
Activate the Microsoft Entra Conditional Access authentication context option and select the previously created authentication context. Save the role setting change with Update.
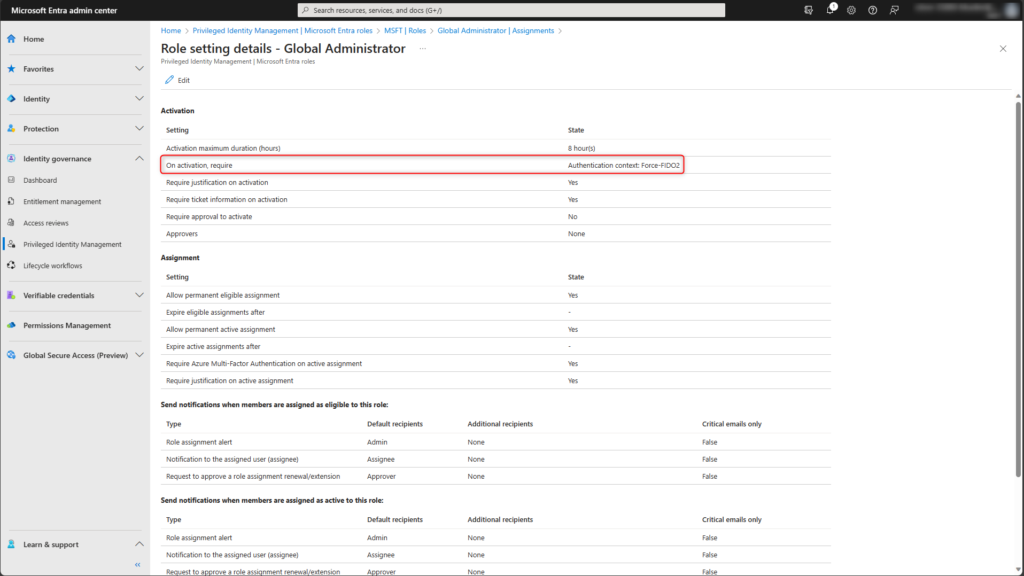
During the privileged role request, the Microsoft Entra conditional access policy is now applied, which is configured to the authentication context.
Test configuration
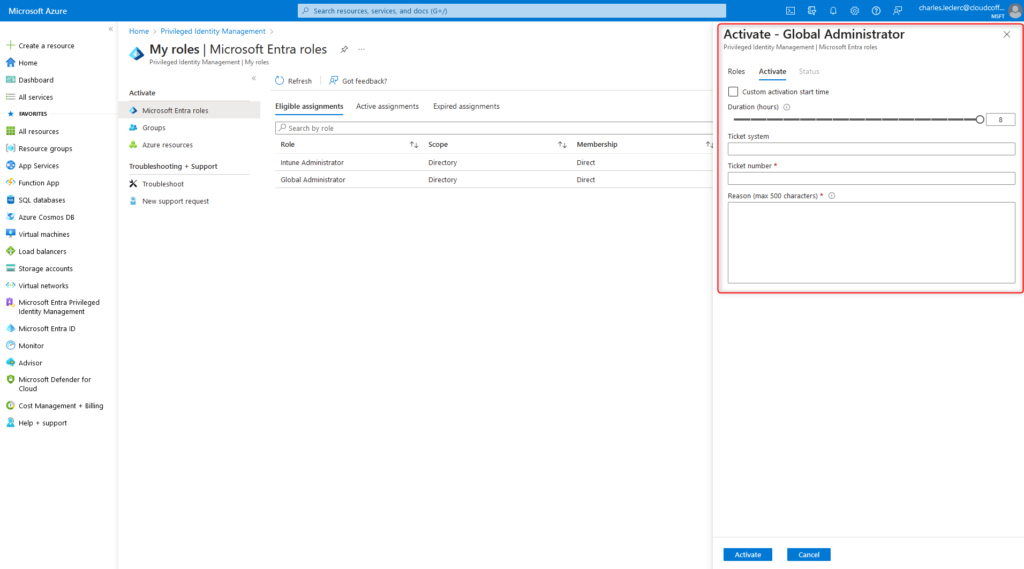
An authorized user requests the privileged role via Microsoft Entra Privileged Identity Management (PIM). The steps required for this process are described in detail in the following link:
Microsoft Entra Privileged Identity Management (PIM): Request Azure Roles by User – cloudcoffee.ch
In this blog post, phishing-resistant multi-factor-authentication is configured for the Microsoft Entra role Global Administrator. When this privileged role is requested, the Microsoft Entra Conditional Access policy ensures that phishing-resistant multi-factor authentication must be performed.
The phishing-resistant multi-factor-authentication is executed by clicking on the message A Conditional Access policy is enabled and may require additional verification.
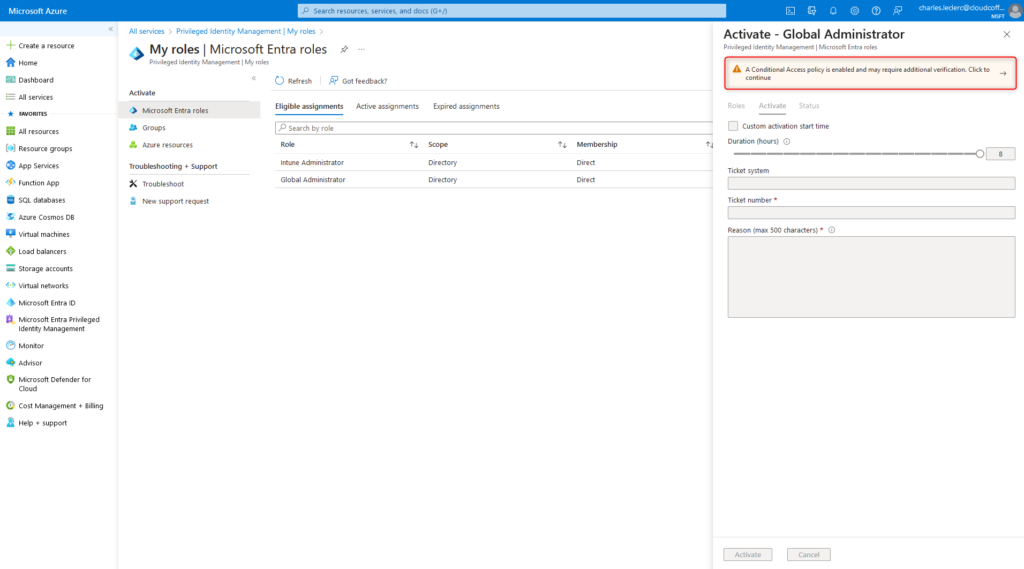
After successful authentication with a phishing-resistant multi-factor-authentication, e.g. a YubiKey FIDO2 security key, the privileged Microsoft Entra role Global Administrator can be requested.