Azure AD Connect: Enforcing TLS 1.2
Azure AD Connect no longer supports the following protocols because they are considered insecure.
- TLS 1.0
- TLS 1.1
- 3DES (TLS_RSA_WITH_3DES_EDE_CBC_SHA)
the following services may be affected by the deactivation of the protocols:
- Azure AD Connect
- Azure AD-PowerShell
- Passthrough Authentication Agents (PTA)
- Applications with Azure AD integration
With TLS 1.2, Azure AD Connect remains executable.
Azure AD Connect as of version 2.0 already requires TLS 1.2 and is not affected by the deactivation of the deprecated protocols.
All versions of Windows Server that are supported for Azure AD Connect V2.0 already default to TLS 1.2. If TLS 1.2 is not enabled on your server you will need to enable this before you can deploy Azure AD Connect V2.0.
Azure AD Connect: TLS 1.2 enforcement for Azure Active Directory Connect | Microsoft Docs
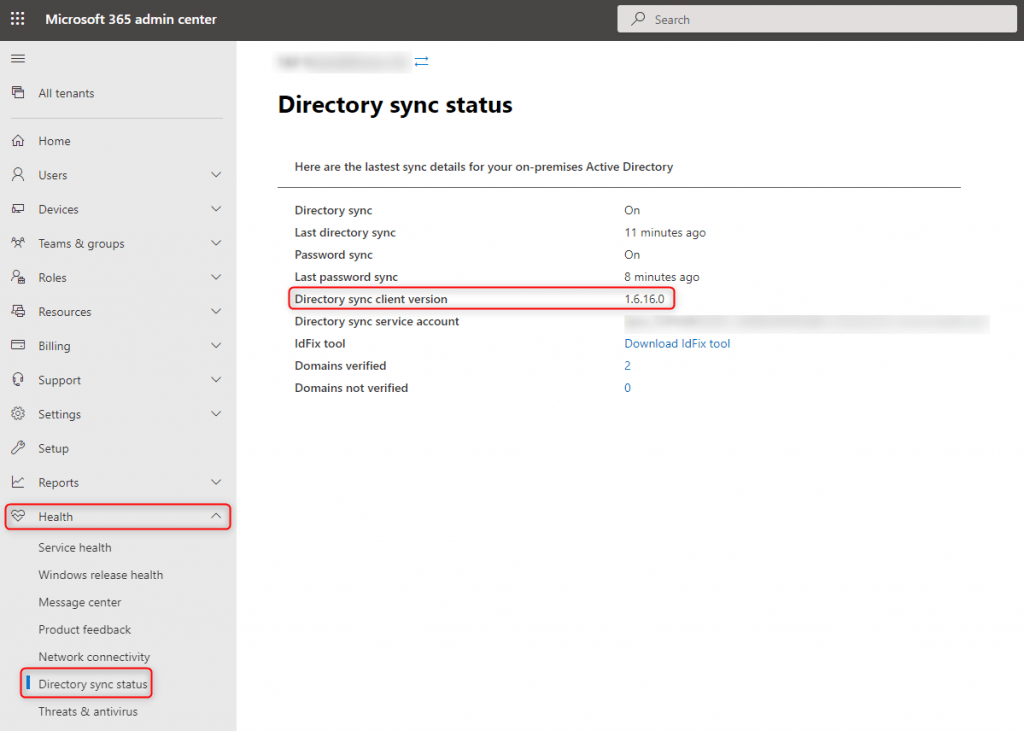
Azure AD Connect: Checking the existing installation
Software Version
The version is shown in MS365 Admin Center (https://admin.microsoft.com) under Health > Directory sync status:
The latest version of Azure AD Connect can be downloaded from the following links:
up to Windows Server 2012 R2:
Latest client version 1.x
https://www.microsoft.com/en-us/download/details.aspx?id=103336
Windows Server 2016 and later
latest client version 2.x
https://www.microsoft.com/en-us/download/details.aspx?id=47594
What TLS version is Azure AD Connect currently using?
Which TLS version does the Azure AD Connect installation really use for communication?
To find out, the network traffic is analyzed. With a network sniffer tool such as Whireshark, the communication of Azure AD Connect is recorded and can be analyzed afterwards.
There are many ways to record network traffic. In our example we use the the “Packet Caputre” function of the Fortigate Firewall and create the required filter for it:
config firewall sniffer
edit 0
set interface "<Interface>"
set host "<LAN-IP Azure AD Connect Server>"
set port "443"
set protocol "6"
next
endNow the sniffer for the recording is started and an Azure AD Full Sync is initiated with PowerShell. This eliminates the waiting time until the next regular synchronization:
Start-ADSyncSyncCycle -PolicyType InitialStop recording after Azure AD Synchronization and open the recorded file with Whireshark.
- Set the filter “frame contains” to “microsoftonline.com”
Azure AD Connect connects to one of the following web addresses during synchronization (see (3) in screenshot):
– https://login.microsoftonline.com
– https://adminwebservice.microsoftonline.com - If there is something other than “TLSv1.2” in the “Protocol” column, you can continue with the following steps.

TLS 1.2
Check necessary registry keys
The following PowerShell script checks if the necessary registry keys are set. This forces communication with TLS 1.2.
(Source: microsoft.com)
Function Get-ADSyncToolsTls12RegValue
{
[CmdletBinding()]
Param
(
# Registry Path
[Parameter(Mandatory=$true,
Position=0)]
[string]
$RegPath,
# Registry Name
[Parameter(Mandatory=$true,
Position=1)]
[string]
$RegName
)
$regItem = Get-ItemProperty -Path $RegPath -Name $RegName -ErrorAction Ignore
$output = "" | select Path,Name,Value
$output.Path = $RegPath
$output.Name = $RegName
If ($regItem -eq $null)
{
$output.Value = "Not Found"
}
Else
{
$output.Value = $regItem.$RegName
}
$output
}
$regSettings = @()
$regKey = 'HKLM:\SOFTWARE\WOW6432Node\Microsoft\.NETFramework\v4.0.30319'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'SystemDefaultTlsVersions'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'SchUseStrongCrypto'
$regKey = 'HKLM:\SOFTWARE\Microsoft\.NETFramework\v4.0.30319'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'SystemDefaultTlsVersions'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'SchUseStrongCrypto'
$regKey = 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'Enabled'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'DisabledByDefault'
$regKey = 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'Enabled'
$regSettings += Get-ADSyncToolsTls12RegValue $regKey 'DisabledByDefault'
$regSettingsIf the PowerShell query outputs the following values from the registry, TLS 1.2 is enabled and no further customization is required.
HKLM:\SOFTWARE\WOW6432Node\Microsoft.NETFramework\v4.0.30319
– SystemDefaultTlsVersions=1
– SchUseStrongCrypto=1
HKLM:\SOFTWARE\Microsoft.NETFramework\v4.0.30319
– SystemDefaultTlsVersions=1
– SchUseStrongCrypto=1
HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server
– Enabled=1
– DisabledByDefault=0
HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client
– Enabled=1
– DisabledByDefault=0

Finally, verify that Azure AD Connect actually uses TLS 1.2: What TLS version is Azure AD Connect currently using?
Force TLS 1.2 with PowerShell
The required registry keys are created with the following PowerShell script.
(Source: microsoft.com)
If (-Not (Test-Path 'HKLM:\SOFTWARE\WOW6432Node\Microsoft\.NETFramework\v4.0.30319'))
{
New-Item 'HKLM:\SOFTWARE\WOW6432Node\Microsoft\.NETFramework\v4.0.30319' -Force | Out-Null
}
New-ItemProperty -Path 'HKLM:\SOFTWARE\WOW6432Node\Microsoft\.NETFramework\v4.0.30319' -Name 'SystemDefaultTlsVersions' -Value '1' -PropertyType 'DWord' -Force | Out-Null
New-ItemProperty -Path 'HKLM:\SOFTWARE\WOW6432Node\Microsoft\.NETFramework\v4.0.30319' -Name 'SchUseStrongCrypto' -Value '1' -PropertyType 'DWord' -Force | Out-Null
If (-Not (Test-Path 'HKLM:\SOFTWARE\Microsoft\.NETFramework\v4.0.30319'))
{
New-Item 'HKLM:\SOFTWARE\Microsoft\.NETFramework\v4.0.30319' -Force | Out-Null
}
New-ItemProperty -Path 'HKLM:\SOFTWARE\Microsoft\.NETFramework\v4.0.30319' -Name 'SystemDefaultTlsVersions' -Value '1' -PropertyType 'DWord' -Force | Out-Null
New-ItemProperty -Path 'HKLM:\SOFTWARE\Microsoft\.NETFramework\v4.0.30319' -Name 'SchUseStrongCrypto' -Value '1' -PropertyType 'DWord' -Force | Out-Null
If (-Not (Test-Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server'))
{
New-Item 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server' -Force | Out-Null
}
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server' -Name 'Enabled' -Value '1' -PropertyType 'DWord' -Force | Out-Null
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Server' -Name 'DisabledByDefault' -Value '0' -PropertyType 'DWord' -Force | Out-Null
If (-Not (Test-Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client'))
{
New-Item 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client' -Force | Out-Null
}
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client' -Name 'Enabled' -Value '1' -PropertyType 'DWord' -Force | Out-Null
New-ItemProperty -Path 'HKLM:\SYSTEM\CurrentControlSet\Control\SecurityProviders\SCHANNEL\Protocols\TLS 1.2\Client' -Name 'DisabledByDefault' -Value '0' -PropertyType 'DWord' -Force | Out-Null
Write-Host 'TLS 1.2 has been enabled. You must restart the Windows Server for the changes to take affect.' -ForegroundColor CyanReboot the server after the PowerShell script is executed.
Finally, verify that Azure AD Connect actually uses TLS 1.2: What TLS version is Azure AD Connect currently using?


