Disabling Basic Auth: Microsoft 365 SMTP Relay for Non-TLS Devices
Last Updated on 20. May 2023
As of October 1, 2022, basic athentication (legacy authentication) will be disabled for EWS, RPS, POP, IMAP, MAPI, RPC, OAB, SMTP AUTH, and EAS protocols in Exchange Online. The basic authentication is a big security issue, since a user name and password are already sufficient for sign in. After deactivating basic authentication, modern authentication (based on OAuth 2.0) becomes active. Modern authentication requires a second factor (multi-factor authentication).
The SMTP AUTH protocol is often used for login by scanners or scripts and multi-factor authentication is not possible. To continue using these services, a Microsoft 365 SMTP Relay can be set up in Exchange Online.
Prerequisites and Licensing
To send email using a Microsoft 365 SMTP Relay, the following requirements must be met:
- Exchange Online is licensed and configured
- Static WAN IP address
- Port 25 (TCP) is not blocked by the firewall and ISP (Internet Service Provider)
An overview of Microsoft 365 license packages with their features can be found at https://m365maps.com.
M365 SMTP Relay Connector Setup
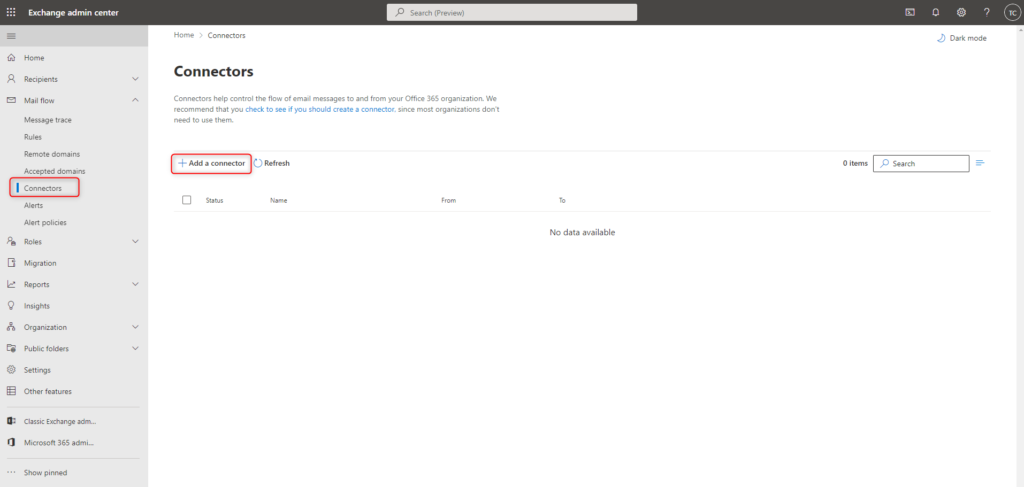
A new Exchange Online Connector is created in the Exchange Admin Center (https://admin.exchange.microsoft.com/).
Exchange admin center > Mail flow > Connectors > Add a connector
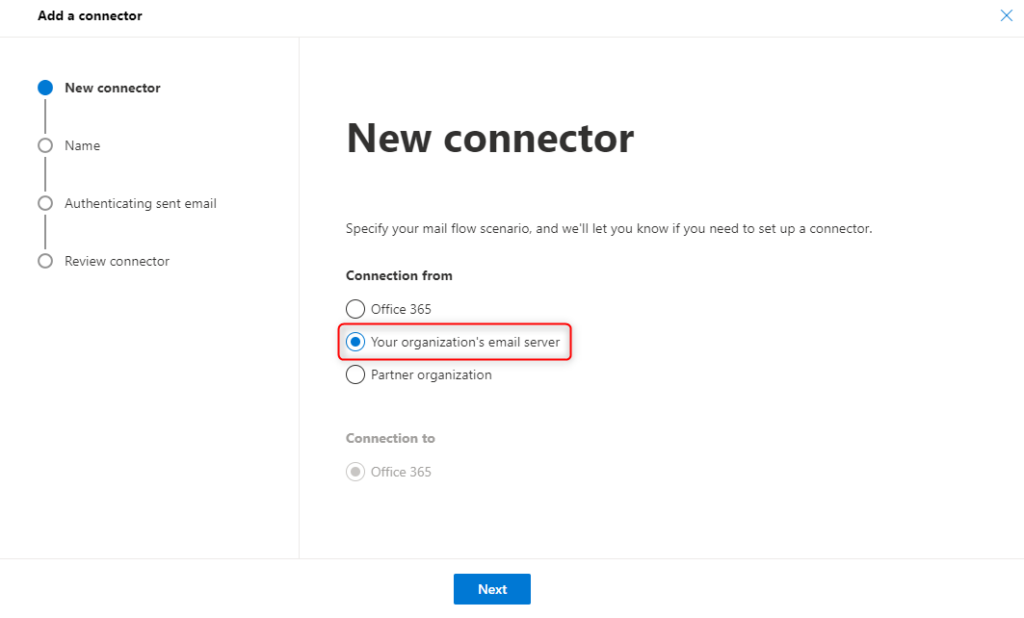
A wizzard for the configuration starts.
The message flow is handled in the Your organization’s email server scenario.
This scenario does not require an email server in the local network. Devices and scripts can communicate directly with this connector after configuration is complete.
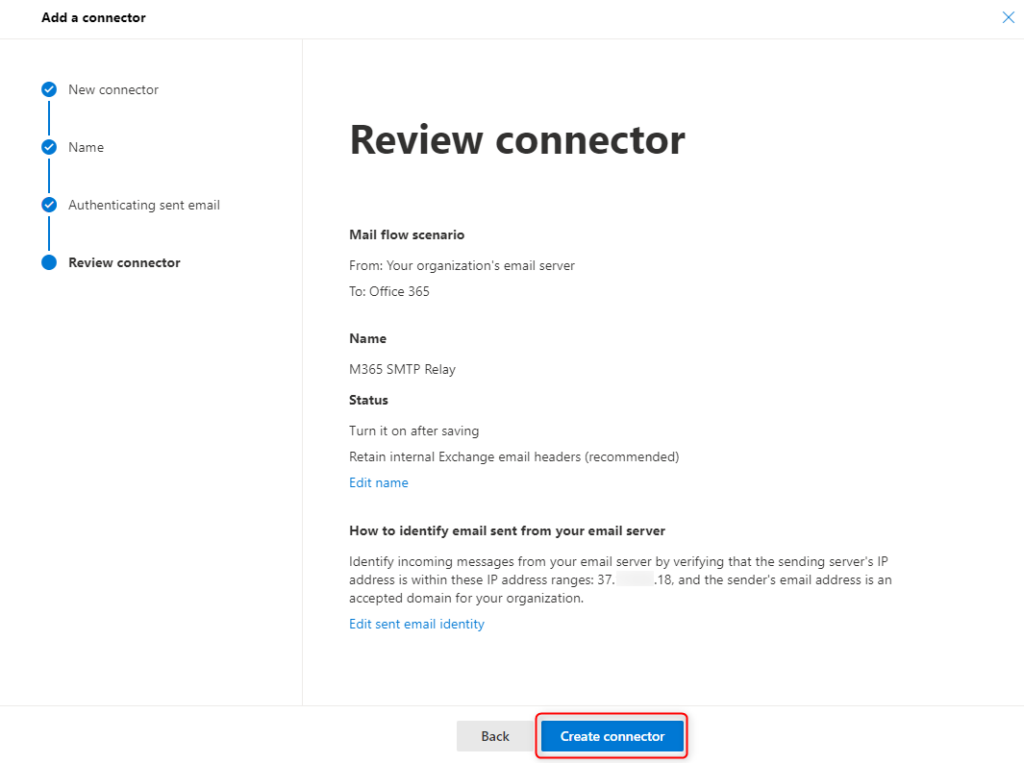
Assign a name for the connector, e.g. M365 SMTP Relay and adjust the options to your own needs.

Authentication at this connector is done via the WAN IP address of the ISP. This means, devices and scripts do not need to perform additional authentication.

Finally, review the settings confirm with Create connector.
After a short time the SMTP relay connector is ready to use.
Client settings for SMTP Relay
The client can access the Microsoft 365 SMTP Relay with the following information. No username or password is required for authentication. Authentication takes place via the WAN IP of the ISP.
| Smarthost | MX-Endpoint e.g. cloudcoffee-ch.mail.protection.outlook.com |
| Port | 25 (TCP) |
| TLS/StartTLS | Enabled |
| Email address | A valid email address from the sender domain The address does not need its own mailbox |
Troubleshooting
Check SMTP Relay with PowerShell
Requirements
- The script is sent over the WAN IP that was specified when the connector was created
- Port 25 (TCP) must be enabled for the client
The following script sends an email via the Microsoft 365 SMTP Relay Connector. change the following placeholders in the script:
(1) SMTP server of the MX endpoint of the sender domain, e.g. “cloudcoffee-ch.mail.protection.outlook.com”
(2) a valid email address from the sender domain
(3) a valid email address of the recipient
$mailParams = @{
SmtpServer = '(1)'
Port = '25'
From = '(2)'
To = '(3)'
Subject = ('SMTP Relay - ' + (Get-Date -Format g))
Body = 'This is a test email using SMTP Relay'
DeliveryNotificationOption = 'OnFailure','OnSuccess'
}
Send-MailMessage @mailParamsThe following email will now be sent to the recipient:

Identify clients with default authentication
In the Azure AD sign-in log, the client apps, which still use basic authentication, can be identified.
See the blog post Block Legacy Authentication with Azure AD Conditional Access – cloudcoffee.ch for more information.


